From the CTO’s Desk – February 2026: Webacy’s Vault Technical Risk Rating System
Structural Risk Beyond Price
In December, we introduced Stablecoin Contamination Monitoring to map how fragility propagates across assets and protocols. In January, we launched the Stablecoin Depeg Risk Monitor to detect early market stress through price instability and volatility signals.
Those systems focused on asset integrity and observable market behavior. However, market signals alone do not describe structural resilience. Vault fragility often precedes volatility. It originates in architectural design choices.
A vault can maintain a stable share price while remaining structurally exposed. Governance design, upgradeability mechanisms, admin key concentration, code integrity, liquidity constraints, and external strategy dependencies shape risk long before it becomes visible in market metrics.
Structural risk is multi-dimensional. It does not originate solely from yield volatility or declining TVL. It emerges from protocol-level design decisions. Examples include:
- Upgradeable proxy contracts that alter trust assumptions
- Externally owned account ownership with unilateral control authority
- Unverified or partially verified contracts that reduce transparency
- Redemption gating or liquidity caps that constrain exit pathways
These conditions are not reliably visible in price charts. They tend to surface only when stress is applied. The objective of this system is to surface structural fragility before it manifests as a market event. The Vault Dashboard operationalizes this framework, providing transparent structural scoring across verified vault infrastructure.
Scope and Objective
The Vault Technical Risk Rating system evaluates ERC-4626 vaults and strategy-based vault contracts across 18 structural dimensions. Each vault receives:
- A composite risk score from 0 to 100, where higher values indicate greater structural risk
- A categorical tier classification
- Structured risk flags
- Transparent sub-ratings across defined risk clusters
The system is designed to measure structural integrity, not performance quality. Yield, momentum, and return optimization are intentionally excluded as primary drivers. Technical fragility and market performance are distinct concepts and are treated separately within this framework.
Verification and Classification
For each vault contract we verified it by conducting bytecode-level analysis to confirm authentic vault structure through:
- ERC-4626 interface detection
- Strategy architecture identification
- Proxy and upgrade pattern recognition
Contracts must exceed a 90% classification confidence threshold and conform to a recognized vault archetype before inclusion. This eliminates token misclassification, prevents false positives from contaminating the dataset, and ensures that only structurally validated vault infrastructure enters the rating engine.
Multi-Signal Rating Framework
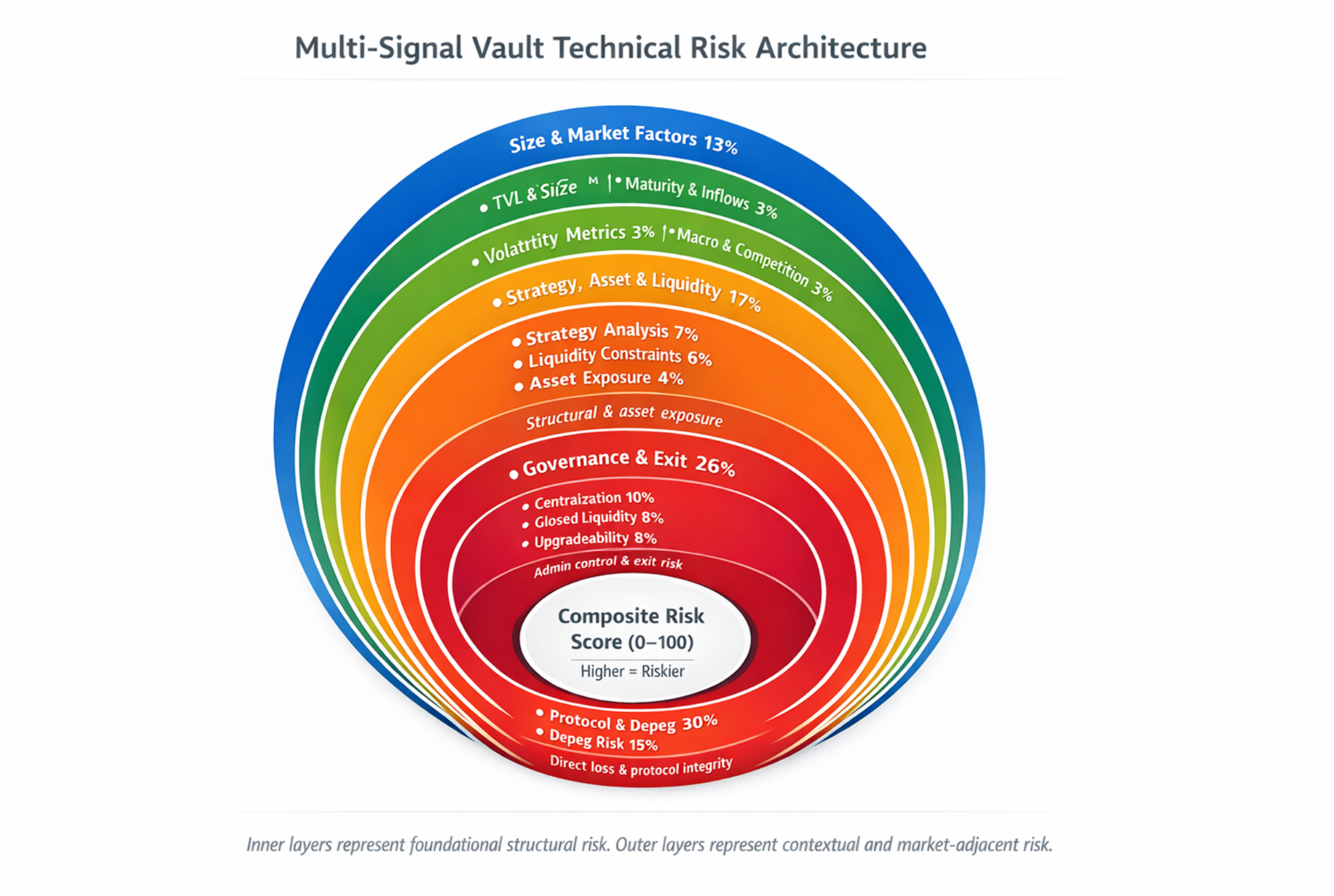
The composite risk score is derived from 18 sub-ratings grouped into five structural clusters. Weighting is intentionally asymmetric to reflect differing levels of structural impact.
The system prioritizes:
- Exit risk
- Governance control
- Catastrophic failure vectors
- Software integrity
Market-adjacent signals are subordinated to structural risk dimensions but still contribute meaningfully to the composite.
Protocol and Depeg Risk
This cluster addresses the most direct vectors of capital impairment and protocol-level structural weakness.
Protocol Risk
We incorporate curated technical assessments aligned with the Trading Strategy Vault Technical Risk Framework. Labels such as Blacklisted, Severe, Dangerous, High, and Low reflect the protocol’s structural condition, including prior incidents, design weaknesses, and systemic dependencies.
Depeg Risk
For stablecoin vaults, deviation from parity is treated as a direct principal risk signal. Sustained breaks below parity indicate structural stress within the collateral, redemption mechanism, or underlying liquidity. Short-lived or minor deviations trigger caution but are not treated as immediate failure states. A stable peg is neutral. Because parity loss directly impacts redeemable value, this dimension carries the strongest influence within the model.
Governance and Exit Risk
Governance configuration determines who controls critical functions and whether capital can exit under stress. This cluster evaluates:
Centralization
Externally owned account ownership, concentrated administrative authority, multisig composition, or pause capability
Closed Liquidity
Disabled deposits, blocked redemptions, withdrawal gating, or queue-based exit constraints
Upgradeability
Proxy patterns, beacon contracts, upgrade hooks, or privileged implementation control
Upgradeable and admin-controlled systems are not inherently insecure. However, they introduce mutable trust assumptions. Those assumptions are explicitly reflected in the risk score.
Code and Security
Contract-level integrity remains a primary structural variable. This cluster evaluates:
Code Patterns
Delegatecall usage, unbounded external calls, verification status, and privileged execution paths
Webacy Code Findings
Reentrancy vectors, unchecked return values, access control gaps, and other vulnerability indicators identified through analysis
Webacy Contract Risk
On-chain behavioral signals such as anomalous transaction patterns, privilege changes, or historical incident linkage
Webacy Deployer Risk
Deployer-level history, prior exploit associations, and systemic behavioral patterns
When critical vulnerabilities are present, this cluster materially shifts the composite score regardless of performance stability.
Strategy and Liquidity Structure
Vaults frequently rely on layered strategy execution and third-party integrations. Each external dependency expands the potential attack surface and failure domain. This cluster evaluates:
Strategy Complexity
Cross-protocol integrations, leverage usage, routing logic, oracle dependencies, and external strategy contracts
Liquidity Design
Lockups, cooldowns, redemption queues, caps, and delayed withdrawal mechanics
Asset Exposure
Asset exposure risk is zero-weighted within the stablecoin vault universe evaluated here, as collateral volatility is external to the structural model.
Size and Market-Adjacent Signals
These signals provide contextual risk framing but do not dominate structural evaluation. This cluster evaluates:
Size: Low TVL fragility and capital concentration risk
Maturity: Newly deployed vault risk and limited operational history
Inactivity: Reduced on-chain activity that may indicate dormant governance or operational stagnation
Return Loss: Negative lifetime performance or sustained underperformance
Drawdown: Historical maximum capital contraction
Sharpe Risk: Weak risk-adjusted performance profile
TVL Outflow: Sustained capital withdrawal patterns
Subvault Exposure: Nested vault or multi-layer strategy dependencies
Volatility: Zero-weighted in alignment with the Trading Strategy framework
Market behavior informs context, but structural design governs the score. The model evaluates how a vault is constructed and controlled before considering how it has recently performed.
Alignment with External Frameworks
The model is built in alignment with the Trading Strategy Vault Technical Risk Framework, which emphasizes software quality, transparency, and a strict separation between market and technical risk. Trading Strategy provides foundational vault data and technical assessments that inform several components of our scoring inputs. We extend those principles within a continuous structural monitoring system. Structural integrity anchors the rating design. The objective is clarity of architecture rather than comparison of returns.
Learning from Vault Incidents
We have also created a Vault Incidents page. It organizes historical vault failures into a taxonomy and maps each event to the relevant risk clusters within our framework. Incidents are categorized by:
- Category, such as vault_contract, strategy_protocol, infrastructure, stablecoin, governance_admin
- Mechanism, such as oracle_manipulation, flash_loan, reentrancy, logic_error, donation_attack
Each incident is mapped to the specific sub-ratings that would have signaled elevated structural risk. Examples include:
- Yearn yUSDT mapped to Code, Upgradeability, and Centralization
- Euler mapped to Strategy and Protocol Risk
- Curve Vyper exposure mapped to Infrastructure dependency
- Morpho Steakhouse mapped to Strategy and Oracle dependency
Building historical datasets is essential for identifying patterns and turning past incidents into practical learning signals.
Needs Attention Filter
A vault is flagged for attention if it meets any of the following conditions:
- Unverified contract
- No audits
- High or Critical tier
- Depeg monitor warning status
This filter is designed to surface priority risks quickly, so monitoring is active rather than passive.
Why This Matters
Vaults now hold billions in user capital. When they fail, it usually is not because the price moved first. It is because something structural was already fragile. That fragility shows up in places like:
- Concentrated admin keys
- Upgrade hooks that change trust assumptions
- Oracle dependencies
- Complex strategy routing
- Redemptions that can be closed under stress
By identifying those conditions early and separating them from day-to-day market noise, the system gives allocators and governance teams a clearer picture of what actually carries risk. This is not a trading signal. It is the infrastructure for understanding how a vault is built.
Conclusion
The Vault Technical Risk Rating system builds on the contamination monitoring introduced in December and the structural stress detection framework launched in January. Together, those systems focused on asset integrity and market-level instability. This model extends that work into vault architecture itself.
It integrates:
- Protocol-level technical assessment
- Bytecode verification
- Smart contract vulnerability analysis
- Governance and exit modeling
- Historical incident classification
The goal is straightforward: identify structural weakness before it becomes visible in price.
We want to give a special shoutout for the support of the Trading Strategy team. Their data infrastructure and vault universe coverage have been foundational to the reliability of this system. We are grateful for their continued collaboration.
As more capital moves into vault systems, understanding how they are built matters as much as how they perform. As vault systems scale in capital and complexity, structural monitoring shifts from optional tooling to foundational infrastructure.